Content
However, it doesn’t have an obvious way of converting assets from hot to cold storage. It is, however, fully open-source — a distinction that only a handful of competitors share. Guarda is a free, all-purpose crypto wallet whose users can access their crypto via mobile, desktop or browser extension. Users of Guarda can move crypto into cold storage through an integration with the hardware wallet Ledger.
- Many or all of the products featured here are from our partners who compensate us.
- On the other hand, the private keys, sometimes called secret keys, give direct access to the wallet and the crypto held within it and thus should never be shared with anyone.
- Although, with that said, you can simply start with a wallet and obtain your cryptocurrency by other means as well (on an exchange, from a peer-to-peer transaction, etc).
- Unlike with traditional investments, digital assets can’t be hidden under your mattress or in a safe deposit box.
- Contrary to popular belief, crypto wallets don’t truly store cryptocurrencies.
- The whole database is stored on a network of thousands of computers called nodes.
- A blockchain is a database of every transaction that has ever happened using a particular cryptocurrency.
By entering your private key, you verify that you own the coins and then you can transfer them to someone else. That is the only way that the coins can move from person A to person B. All examples listed in this article are for informational purposes only.
Are Crypto Wallets Anonymous?
They typically come with additional security features, such as a PIN code or biometric authentication, and can support multiple cryptocurrencies. However, hardware wallets can be more expensive than software wallets. They can also be more cumbersome to use, as they require you to connect the device to your computer or smartphone whenever you want to make a transaction.
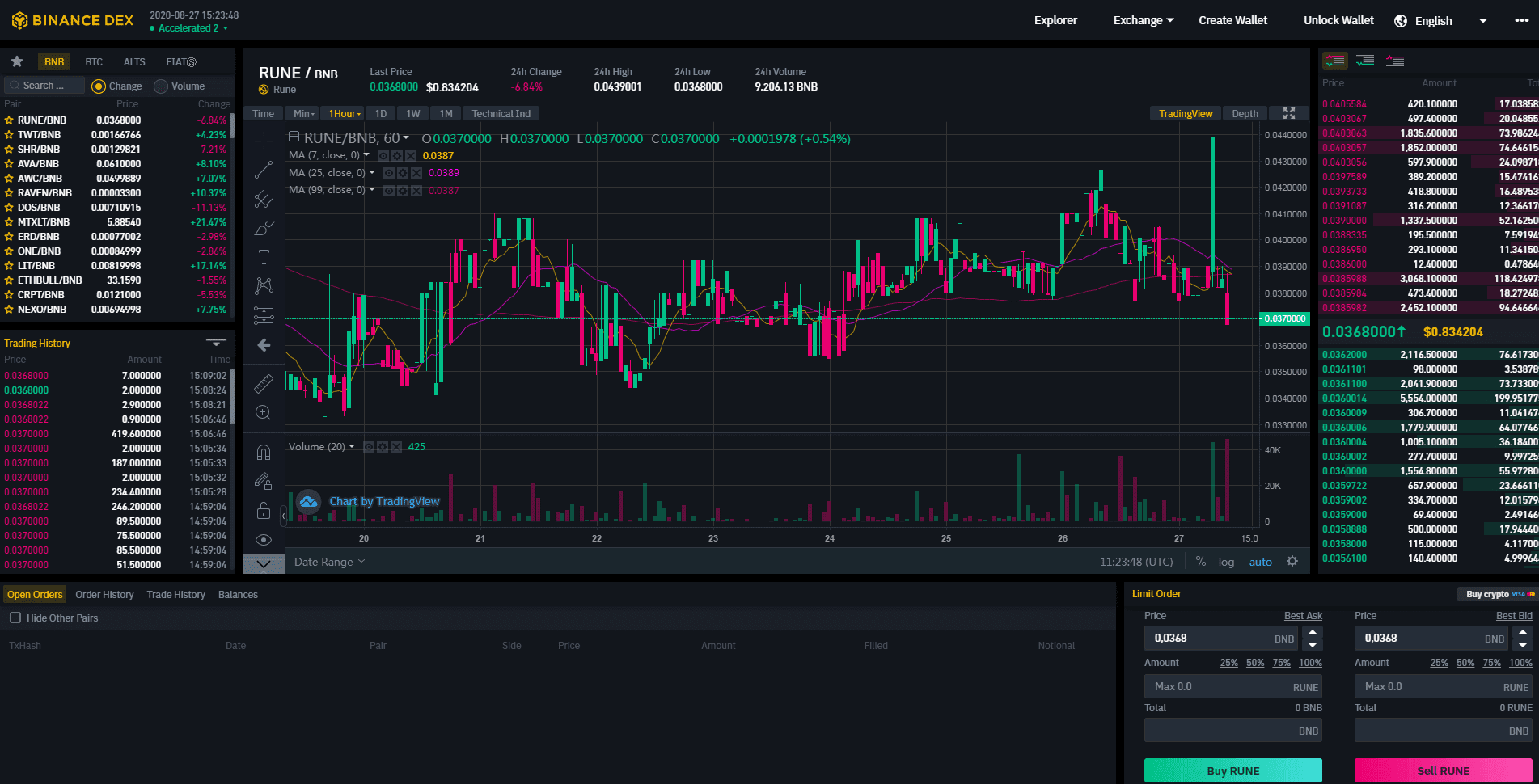
Hardware wallets provide an extra layer of security for your private keys, as they are stored offline and are, therefore, less vulnerable to hacking and cyber-attacks. Additionally, most hardware wallets have additional security features, such as a PIN code or biometric authentication, to further protect your digital assets. Even if the physical device is stolen, without the PIN or biometric what is a crypto wallet authentication, your assets cannot be retrieved using another device’s recovery key. As a way to protect users’ funds, Binance only holds a small percentage of coins in its hot wallets. The remaining is kept in cold storage, disconnected from the Internet. Noteworthy, Binance DEX provides an alternative for users that prefer not to keep their funds in a centralized exchange.
One common way cryptocurrencies are created is through a process known as mining, which is used by Bitcoin. Bitcoin mining can be an energy-intensive process in which computers solve complex puzzles in order to verify the authenticity of transactions on the network. As a reward, the owners of those computers can receive newly created cryptocurrency. Other cryptocurrencies use different methods to create and distribute tokens, and many have a significantly lighter environmental impact. Hot wallets are used to conduct transactions in digital currencies. Learn how they work, if they’re secure, and what you can do to secure your cryptocurrency.
Cryptocurrency Wallet: What It Is, How It Works, Types, Security
The offers that appear in this table are from partnerships from which Investopedia receives compensation. Investopedia does not include all offers available in the marketplace. However, there is nothing wrong with using a paper wallet if you take measures to store it properly in a safe or deposit box and check on it once in a while to ensure it hasn’t deteriorated. Meanwhile, web-based wallets are mostly accessible through browsers and let you transact anywhere you have an internet connection, he says. More and more cryptocurrencies are being added all the time, however, to check which coins they support, you can click the link here.
A web wallet offers the greatest level of convenience when sending coins to another person, however, they are also the least secure. This is because the wallet provider usually has full control over it. However, a cryptocurrency wallet address does not reveal the real-world identity of its owner, which is why the blockchain is referred to as “pseudonymousâ€.
Trade Bitcoin for Free, use leverage, and get all current welcome bonuses at Bybit with referral code CCFsignup. Sign up and we’ll send you Nerdy articles about the money topics that matter most to you along with other ways to help you get more from your money. For lucky miners, the Bitcoin rewards are more than enough to offset the costs involved.
Are NFTs cryptocurrencies?
Unfortunately, if something goes wrong with the exchange, the user’s crypto may be in jeopardy. In essence, the exchange holds the user’s private keys, which can be likened to the phrase “not your keys, not your coinsâ€. Hardware wallets provide a secure way to store and manage your private keys, keeping them offline and out of reach of hackers and scammers. By generating and storing your private keys on a hardware device, you can be sure that your digital assets are safe and secure while you sleep at night.
Paper wallets, or pieces of paper with a QR code or private key printed on them, fall into this category as well. These have largely gone out of fashion as other types of wallets offer safer and easier-to-use options. So, the term ‘wallet’ is somewhat of a misnomer, as crypto wallets don’t actually store cryptocurrency in the same way physical wallets hold cash. Instead, they read the public ledger to show the balances in a user’s addresses, as well as hold the private keys that enable the user to make transactions. While cold wallets are more secure than hot wallets, they are also less convenient.
Do I Need a Wallet for Cryptocurrency?
The device is never connected to the internet unless you need to transfer funds. However, you enter your private pin directly on to the device, making it virtually impossible for a hacker to access your keys. So, now that you have a basic understanding of what a cryptocurrency wallet is used for, I’ll explain in more depth how it works. On the flip side, this means that users must be in charge of their own security with regard to the storage of passwords and seed phrases.
When you want to transact or check your balance, you simply plug in the device and enter your PIN code to access your wallet. Since anyone can remove funds from an address with that address’s matching private key, it’s critical to protect your private key information. You can generate many public keys — each with their https://xcritical.com/ own separate receiving address — from one private key. This “one-way†— or “trap-door†— encryption, makes it possible to share a public key without worry that someone will figure out your private key and steal your crypto. Crypto wallets all begin with a private key, a long, randomized string of letters and numbers.
Essentially, different wallets offer different things, such as extra security, user-friendliness or convenience. I will now list the most popular types of cryptocurrency wallets. “Most Crypto wallets allow users to send, receive, and store crypto. Some have a feature to buy and spend cryptocurrencies,” says Utsav Dar, co-founder of Incub8 Finance. “Certain crypto wallets have additional features like swapping between tokens, staking tokens for a fixed return paid out to users, as well as access to dApps built on various networks.” Consider types of cryptocurrency wallet that use multisig technology like a shared bank account, where all parties need to enter their PIN or order to complete a transaction. A multisig wallet is ideal for use by families and businesses alike.
What is Cryptocurrency: Your Complete Crypto ABC
However, if you are just getting started with cryptocurrency and are investing a smaller amount, a digital or exchange wallet may be sufficient for your needs. Private keys are crucial to the security and ownership of your cryptocurrency, as they are the only way to prove that you are the rightful owner of your digital assets. If your private keys are lost, stolen, or compromised, you may lose access to your cryptocurrency forever, with no way to recover your funds. Hardware wallets generate and store your private keys in a secure, offline environment. Private keys are the passwords that allow you to access your cryptocurrency, and they must be kept secret and secure at all times.
Understanding Airdrops and Lockdrops: Key Considerations for Cryptocurrency Investorshttps://t.co/Jjk15ToV1I#Airdrop #Lockdrop #Cryptocurrency #Token #Coin #Wallet #Addresses #Social #Media #Eligibility #Requirements #Due #Diligence #Smart #Contract #Long #term #Holding pic.twitter.com/WMN9OnWU4q
— Alex M C AB (@AlexMarknadsfr1) January 7, 2023
This is not something you want to leave to chance; if you lose access to these “private keys,†you may never get your cryptocurrency back. To overcome the lack of accessibility, you can use Binance DEX to connect your device directly to the trading platform. This is a secure way of accessing your funds because the private keys never leave your device.
A software wallet is a computer program or mobile app that holds private keys online. Software wallets are unique to each cryptocurrency while hardware wallets often support multiple currencies . Cold wallets are a crypto wallet type used for the “cold storage†of cryptocurrencies, and are stored offline for improved security. They’re more like a real-world safe or a vault than a leather wallet you carry with you for day to day transactions.
Web3 has a user experience problem
Some crypto holders opt for paper wallets as a means of long-term cold storage as they are not prone to device failure that modern technological devices can sometimes incur. Decentralized finance is an umbrella term for a variety of financial applications provided through digital assets. Because digital assets live on the blockchain, we can access and manipulate them via code in smart contracts. This enables infinite possibilities to automate complex transactions and financial activity where the digital assets are the medium of exchange.
If you don’t manually set the change address to one that you control, you will likely lose your funds. For example, imagine that you generated a paper wallet and sent multiple transactions to fund it, summing a total of 10 BTC. If you decide to spend 2 BTC, you should first send all 10 coins to another type of wallet (e.g., desktop wallet), and only then spend part of the funds .
Blockchain technology could be used for elections in some of the most corrupt countries in the world. Free elections could be held without fear of violence or intimidation. Thirty percent of UN Aid is lost to third-party corruption so UNICEF has been using Ethereum to raise money for the children of Syria.